Limit access using Security Groups
Always grant the minimum required permissions in Security Groups (least privilege).
Check that granted permissions are as desired, as developers often create open security groups for testing and forget to close them before moving them to production.
AWS Config provides rules such as restricted-ssh that can be used to detect Security Groups that have SSH access open for any IP, which is not good practice. We recommend using AWS Systems Manager Fleet Manager that does not require opening any inbound ports, or the use of hardened bastions.
If you handle loads with Microsoft Windows, you can take advantage of AWS Systems Manager Session Manager to use Powershell, but you require bastions to access via Remote Desktop Access (RDP). You can use the AWS Config restricted-common-ports rule by indicating port 3389 as one of the parameters to detect open RDP ports.
Use references in security groups
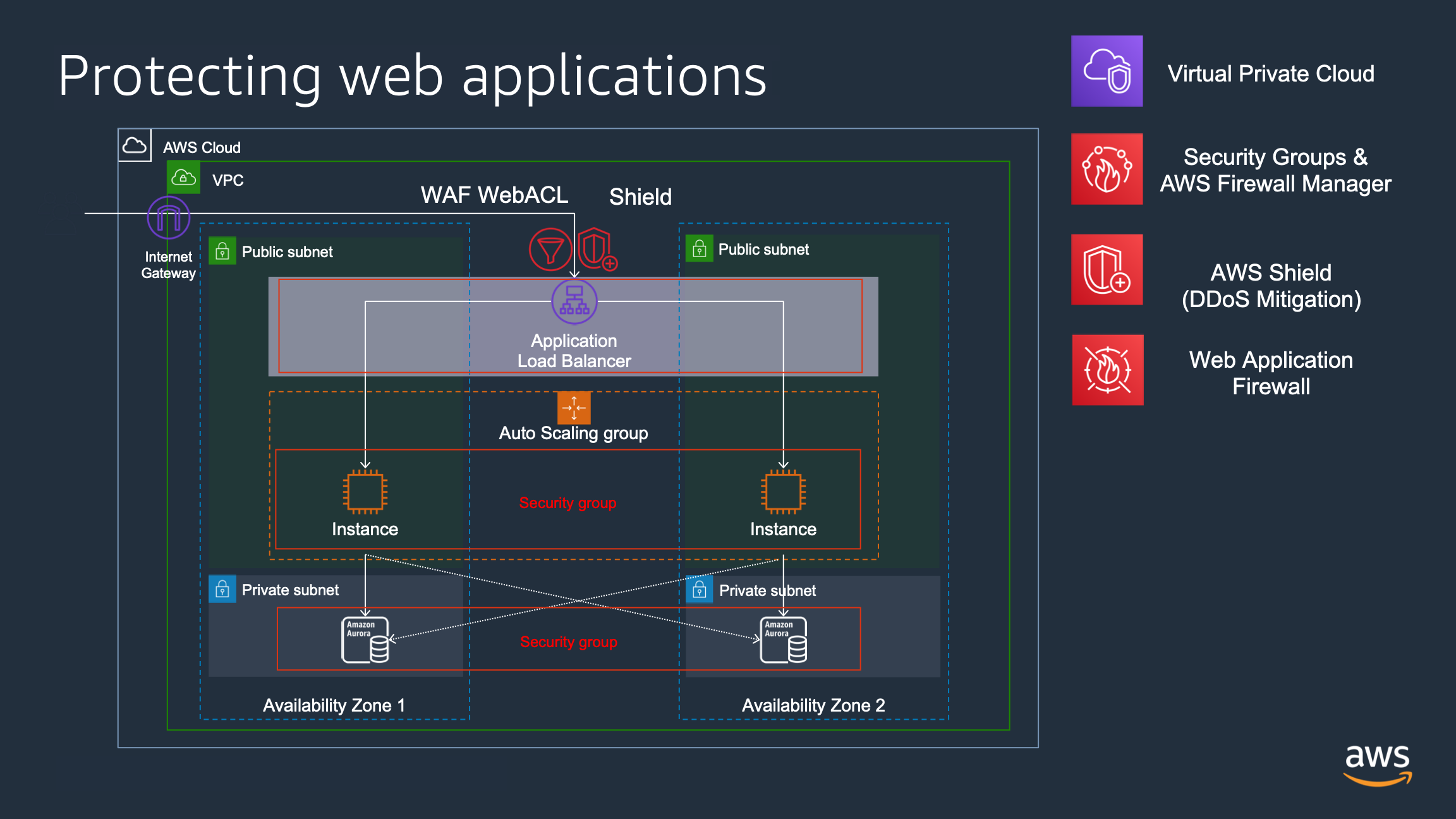
Another recommendation is the use of references in security groups, for example, in a web application:
- An Application Load Balancer with Security Group “sg-alb” allows inbound connections to port 80/443
- An Autoscaling group with web servers in multiple availability zones using Security Group “sg-webservers” allowing traffic to port 80/433 only from resources using Security Group “sg-alb” (only from load balancer).
- A database service, such as Amazon Aurora or Amazon RDS configured with a Security Group “sg-db” allowing traffic to port 3306 only from instances with Security Group “sg-webservers”.
Thus in this way, web instances only serve traffic that comes from the ALB (where you can configure AWS WAF , ensuring that all inbound traffic to web instances has been inspected. The database service only serves requests from web servers, and if a new instance is added by autoscaling, it will be added to the security group and will be able to access the database.